How to Remove Malware from your Site

Taking over an existing site for a client which is infected with malware can be a complex mess to deal with and to get the site clean and free of malware. Luckily there are a number of security and malware scanning plugins that will help with being able to clean up the site.

The iThemes Security Pro plugin includes a number of security features and includes a site scanner that will scan WordPress core and plugins for files that should not exist on the site.

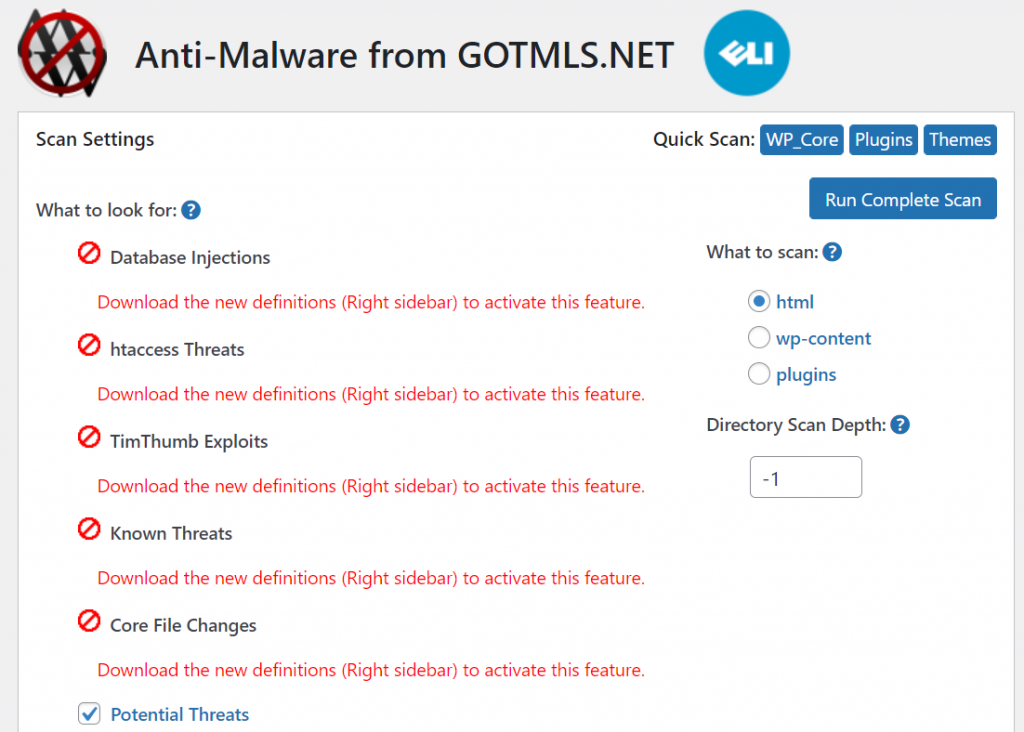
Anti-Malware Security and Brute-Force Firewall is a plugin that makes it very easy to scan a site in order to find infected files and the most common files that should not exist on the site. Using the plugin you can run quick scans in WordPress core, plugins, or themes or scan all files in the html (public_html in some cases) of the site’s server.
Another recommended plugin for easy site scanning would be Malware Scanner which includes options for running quick or standard scans of the site.

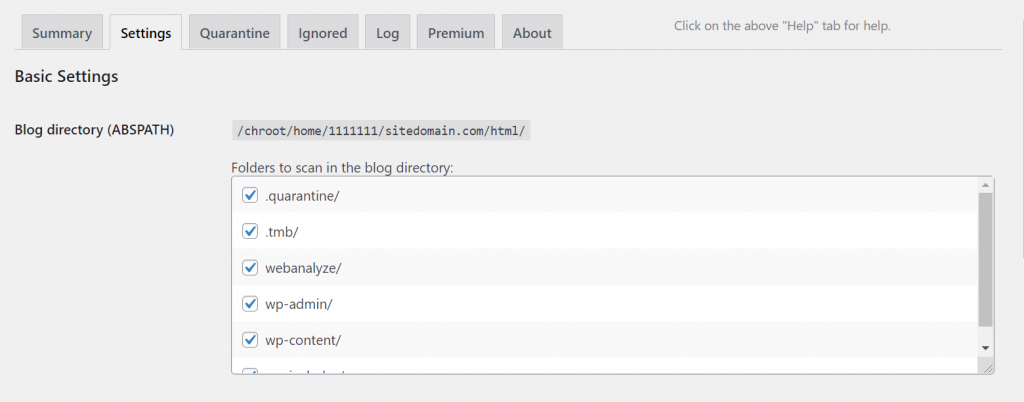
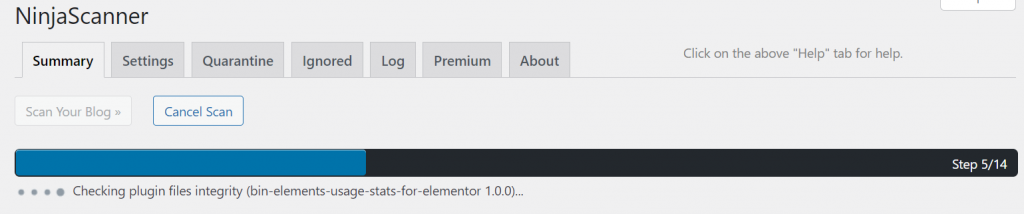
A final plugin recommendation would be in using the NinjaScanner plugin. Within the plugin settings, you can set which folders to include when you run a scan on your site as well as which email address to use for sending the site scan report to.
All of these plugin options will help show which files should not exist in WordPress core, plugins, and themes on the site. Then once you have found the files which should not exist by deleting the files that should not exist in plugins. Plugins would be recommended to be updated if they are outdated since one of the most common attack vectors on a site would be outdated plugins. You could delete existing plugins that contain files that do not exist either from wp-admin or directly with SSH access for the site’s server. Then you would need to install the plugins which have been deleted on the site.
Themes that have been infected if the theme exists on WordPress.org then you could delete the existing theme after setting the site to use a default theme like say Twenty Twenty-One. If the parent theme being used on the site is a premium theme like any of the themes sold on Envato that was infected then you would need to have the client provide the most zip file of the theme then install the theme again on the site. Theme settings would not be lost since they would be saved in the site’s database.
WordPress core files that should not exist it would be recommended to first create a backup before you delete any files. The next step would be deleting files that should not exist in WordPress core some common files that might be added if the site was infected would show as random folders added into WordPress core folders or random PHP files in the html folder of your site and within WordPress core folders or .htaccess files within WordPress core folders.
It is also recommended to shuffle salts in the sites wp-config.php file. If you are using the iThemes Security plugin then you can already easily shuffle salts without having to manually make the change. Then you should update the database password being used in the sites wp-config.php file which in most cases you can change the database password in the portal/manager of the site’s host then copy the new password and update the database credentials in the site wp-config.php file. Also, look if there is a phpinfo.php file or similar then it recommended deleting that file.
These are the most general steps to remove and clean up malware found on an existing site, there could be other attack vector methods that the hacker might have used on the site. But the most common ones are outdated plugins and themes which then leave the site exposed and then WordPress core is altered to become infected. There are a number of WordPress common hacks that might have been run on the site.
Share
Manage Unlimited WordPress Sites from One Dashboard!
- Privacy-first, Open Source, Self-hosted
- Easy Client Management
- 15+ & 30 + Premium Add-ons
- Bulk Plugins & Themes Management
