Social Warfare Plugin Vulnerability Temp Deactivate Now

If you are using the Social Warfare plugin on any child sites (including the pro version of the plugin), deactivate the plugin on any child sites and wait for an update to be released. Wordfence has more about the issue in the plugin, which states that it is a stored Cross-Site Scripting (XSS) vulnerability. Sucuri also put out a post about the specific issue. Wordfence has updated the original post to include more information about the attack and what exactly was happening.

The plugins downloads have been temporarily closed at WordPress.org. The only other information about the issue is that the plugin when active is causing malware and/or sites to redirect. The issue is effecting live sites on versions 3.5.1 and 3.5.2. The current version of the plugin is 3.5.4.
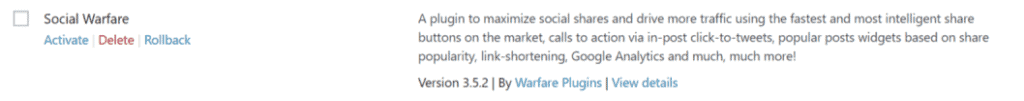
The developers of the Social Warfare plugin are aware of the zero-day exploit and a new release 3.5.3 should be updated on WordPress.org in the next hour, if not sooner.
Update
On the afternoon of March 21, 2019, we were made aware of Zero-Day vulnerability affecting websites using the Social Warfare plugin.
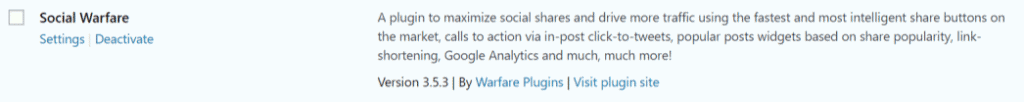
Our development team has submitted Social Warfare V3.5.3 to the WordPress update-repository, which addresses this vulnerability and undoes any changes it makes. Please log-in to your WordPress dashboard and apply this update as soon as possible.
You can also manually download and install these updates directly via these links:
Social Warfare
https://warfareplugins.com/updates/social-warfare/social-warfare.zip
Social Warfare Pro
https://warfareplugins.com/updates/social-warfare-pro/social-warfare-pro.zip
If you are not able to immediately apply this update we recommend that you disable Social Warfare and Social Warfare Pro until you can apply the V3.5.3 update.
Version 3.5.4 of the plugin has been updated on WordPress.org, so the recommended action is to update Social Warfare as soon as possible. Any malicious eval() option values will be deleted in the plugin update.
The WP-CLI command to update the plugin is;.
wp plugin update social-warfare
Wordfence published an additional post about the other vulnerability that was discovered in version 3.5.2 of the plugin, which was allowed remote code execution (RCE)
Share
Manage Unlimited WordPress Sites from One Dashboard!
- Privacy-first, Open Source, Self-hosted
- Easy Client Management
- 15+ & 30 + Premium Add-ons
- Bulk Plugins & Themes Management
