Since more than a dozen privacy laws can apply to a business website, many business owners have been looking for ways to standardize their Privacy Programs.
Standardizing your Privacy Program can help you quickly identify the privacy laws that apply to you, evaluate their requirements, determine the steps you need to take, and, crucially, avoid duplicate work.
In addition, a standardized Privacy Program can help you integrate new technologies and evaluate and mitigate risks.
So how do you standardize a Privacy Program? Thankfully, you do not have to start from scratch and can instead work off of the National Institute of Standards and Technology (NIST) Privacy Framework.
The Framework was created specifically to help organizations build consumer trust with privacy-conscious design and deployment, meet compliance requirements, and reduce risk.
In this article, we will discuss how you can use the NIST Privacy Framework to help you comply with privacy laws, including the structure of the Framework, making adaptations for certain requirements, and practical tips.
Disclaimer: The information in this article is provided for awareness purposes only and should not be construed as legal advice. Consult your attorney for legal matters.
What is the NIST Privacy Framework?
The NIST Privacy Framework is a voluntary tool organizations can use to manage their Privacy Programs. The fact that the Framework is voluntary means that you are not required to use it but can use it if you would like.
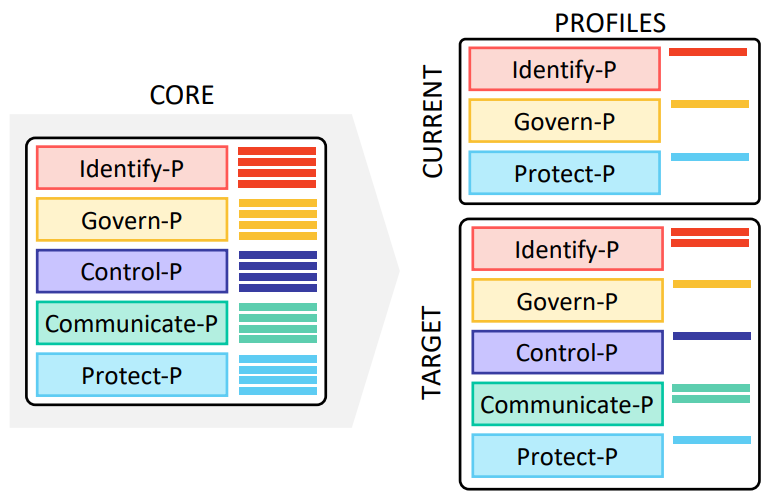
The Framework is divided into three parts:
- The Core: a set of privacy protection activities and outcomes that enable a dialogue about managing privacy risk;
- Profiles: a listing of the business’s current privacy activities and desired outcomes;
- Implementation tiers: a point of reference on how a business views privacy risk and whether it has sufficient processes and resources to manage that risk.
1. NIST Privacy Framework: The Core
The first step of the NIST Privacy Framework is the Core, the purpose of which is to start your business by discussing the management of privacy risk. The Core discusses the following functions:
- Identify: Develop the organizational understanding to manage privacy risks for individuals arising from the processing of their personal information;
- Govern: Develop and implement the organizational governance structure to enable an ongoing understanding of the organization’s risk management priorities;
- Control: Develop and implement appropriate activities to enable organizations or individuals to manage data and thus manage privacy risks;
- Communicate: Develop and implement appropriate activities to enable organizations and individuals to have a reliable understanding and engage in a dialogue about how personal information is processed;
- Protect: Develop and implement appropriate data processing safeguards;

Source
Those familiar with privacy law requirements will immediately see the value of the Core for compliance with privacy laws.
For example, the identify function of the Core asks businesses to inventory systems, products, and services where personal information is processed.
If you need to comply with privacy laws such as GDPR that provide individuals with the right to ask for their data to be deleted, an accurate inventory of where that data is stored will help you quickly delete that data.
In addition, the identify function asks businesses to inventory the purposes for data processing, which will help businesses process the data only for the purposes for which it was collected, a requirement of multiple privacy laws.
Another example of how the NIST Privacy Framework maps to privacy law compliance requirements is that the governing function of the Core asks businesses to have organizational privacy values and policies, such as a Privacy Policy, which is a requirement under multiple privacy laws.
It is important to note that the Privacy Framework does not state what disclosures the Privacy Policy needs to contain. Hence, it is important that you map that requirement with the disclosures required by the privacy laws that apply to you to achieve full compliance.
The control function in the Core also provides that you must have processes in place for enabling privacy rights requests, a common feature of almost every privacy law.
However, you should ensure that those processes reflect the requirements of the privacy laws that apply to you, such as the timeframe for response and the requirements of the response, such as the requirement to notify individuals that they may have the right to appeal any privacy rights decisions.
Lastly, the protect function enables organizations to adequately protect the personal information they collect. This function includes various technical and organizational measures to protect personal information, which is also a common requirement of various privacy laws.
In fact, certain privacy laws, such as the Tennessee Information Protection Act, specifically state that meeting the requirements of the NIST Privacy Framework can be a safe harbor for businesses, so using the framework can help you with compliance with privacy law requirements, as long as you add those requirements into the Framework.
2. NIST Privacy Framework: Profiles
The Profiles section of the Framework takes the functions, categories, and subcategories from the Core to describe the current state and the desired state of specific privacy activities.
A Current Profile indicates the privacy priorities currently being achieved, while a Target Profile indicates the privacy priorities that must be achieved to meet the desired goals.
Organizations must then compare the Current Profile and the Target Profile to see if there are any gaps that must be filled to achieve full compliance and the desired goals. The organization can then take those gaps and come up with a plan to fill them.
For example, if an organization currently knows that it needs to provide certain privacy rights to individuals but does not have a process in place for responding to privacy rights requests, that would be considered a gap that would need to be filled.

Source
3. NIST Privacy Framework: Implementation Tiers
The final step in the NIST Privacy Framework is to place risks into tiers so that proper resources can be allocated to each gap.
The Framework includes four tiers: partial (tier 1), risk-informed (tier 2), repeatable (tier 3), and adaptive (tier 4).
The tiers range from limited awareness and understanding of privacy requirements and risks to organizations that adapt privacy practices based on requirements, lessons learned, and the identification of new privacy risks.
The implementation tiers are used to determine what resources should be allocated to which Privacy Program gaps so that the most urgent and needed gaps are filled first.
When using the NIST Privacy Framework to comply with privacy laws, it is important to follow the above parts of the Framework while also adapting those parts to the hard requirements of privacy laws.
Since the Framework is not based on any particular privacy law, adaptations will be necessary to ensure that all points of compliance requirements are covered.
Thankfully, NIST also provides “crosswalks” – documents that outline and map multiple privacy laws, standards, and other frameworks to the NIST Privacy Framework, which can help you save a lot of time.
Finally, the Framework is a helpful tool to standardize your Privacy Program but is not a replacement for the advice of a privacy attorney, so you should ensure to combine privacy law requirements and the Framework.