How to Scan for Files That Should Not Be In Your WordPress Install

Backup files such as MySQL dumps, and wp-config.php backup files should not be stored in your WordPress install’s public_html (root folder).
It’s important to note that the backup wp-config.php file can provide an easy way for a site attacker to find the database credentials.
These credentials can then be used to directly connect to your site to insert content in the site’s database or to create an admin user to install and deploy malicious content to your site from plugin installs.

One of the easiest security plugins to scan for those types of files is Wordfence.
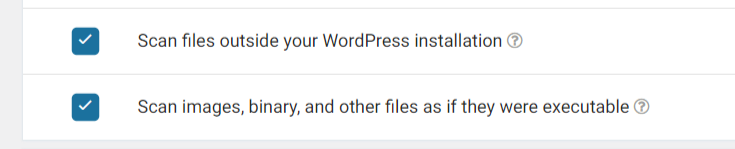
To ensure that files outside of your WordPress installation are included in the Wordfence site scan, you’ll need to enable that option in wp-admin by going to:
Wordfence > All Options
When you go back to run an on-demand scan or wait for the site scan to run in the set schedule, files outside of the WordPress installation will be included in the scan.
You can also set images that could be executable files but renamed as image files to be included in the scan. Both of those site scanning options will need to be enabled since they are not enabled by default in site scanning options.
To access site scan results and start an on-demand scan in Wordfence in wp-admin, go to:
Wordfence > Scan
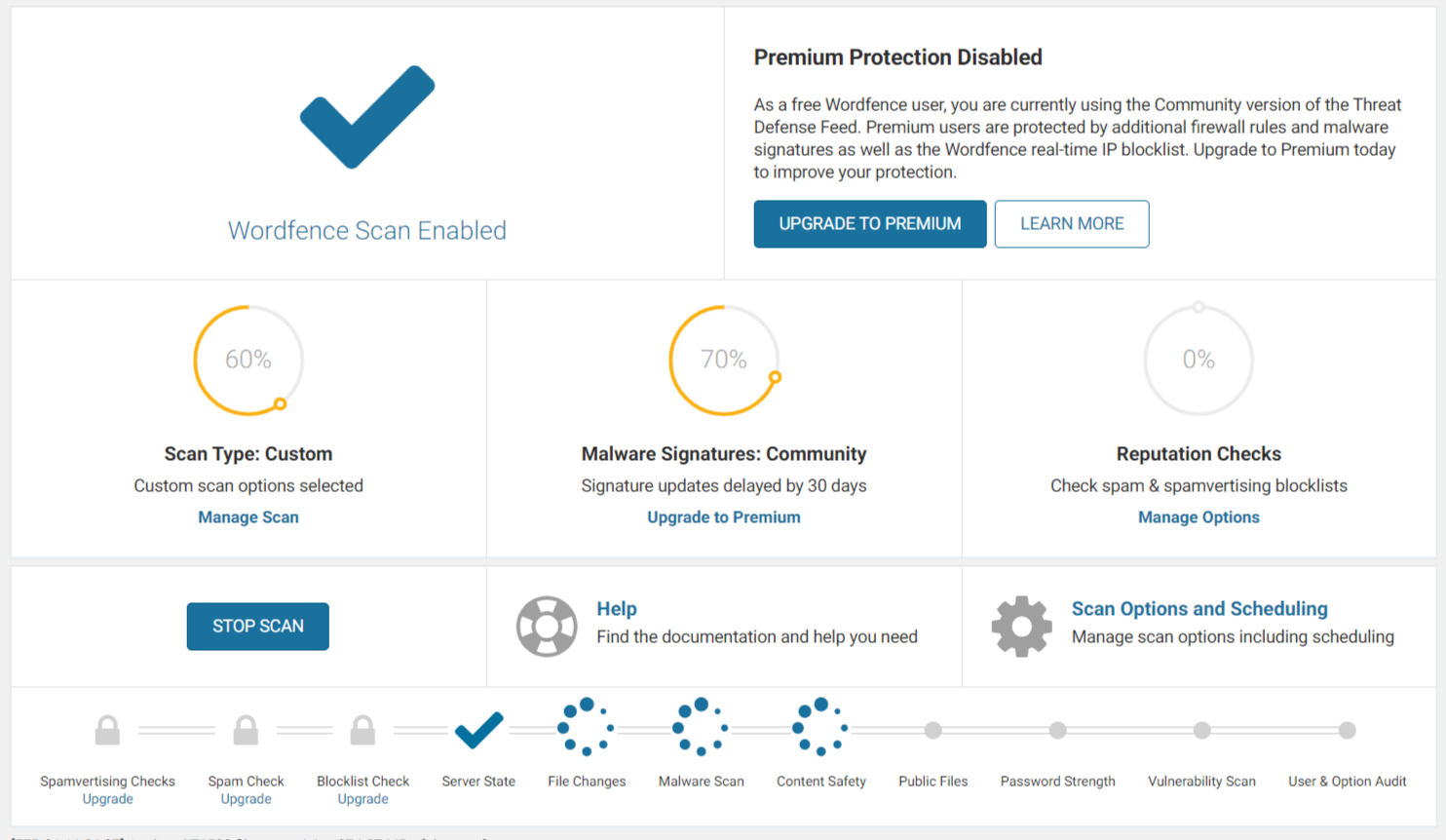
If any files are found that you do not recognize, or if the scan results show that you have a backup or other files that should not be stored on the site’s server, it is recommended to delete them.
Useful Links
Share
Manage Unlimited WordPress Sites from One Dashboard!
- Privacy-first, Open Source, Self-hosted
- Easy Client Management
- 15+ & 30 + Premium Add-ons
- Bulk Plugins & Themes Management